需求:已經熟悉 CentOS 6 的 AD 加入方式,CentOS 7 已將 winbind 改成 sssd,並預設使用 sssd,但還想使用舊的 winbind。
(在 AD 統一控管帳號之環境中,將 Linux 伺服器加入 AD,以使 Domain Admins 群組成員可以登入操作 Linux 伺服器,毋須於 Linux 系統中另行建置帳號。)
一、安裝需求套件:
# yum install -y samba samba-common samba-client samba-winbind* krb5-workstation ntp
二、設定開機時啟動服務:
# systemctl enable smb
# systemctl enable winbind
三、修改 /etc/hosts :
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
123.123.123.123 myhost myhost.mydomain.com.tw
2001:1234:1234:1234::123 myhost myhost.mydomain.com.tw
四、修改 /etc/sysconfig/network-scripts/ifcfg-eth0 :
DNS1=123.123.123.111 (AD Controller 的 IP)
五、修改 hostname :
# hostnamectl set-hostname myhost.mydomain.com.tw
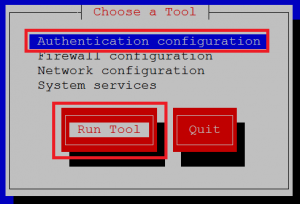
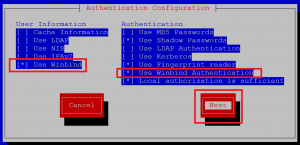
六、執行 setup 比較方便,但 CentOS 7 預設沒裝,我們可以自己裝 setup 套件:
# yum install -y setuptool ntsysv system-config-network-tui system-config-firewall-tui authconfig
# setup
七、修改 /etc/samba/smb.conf ,增加下列設定:
encrypt passwords = yes
winbind enum users = yes
winbind enum groups = yes
template homedir = /home/%D/%U
八、修改 /etc/nsswitch.conf 設定,將 winbind 的順位放到 sss 前面:
passwd: files winbind sss
shadow: files winbind sss
group: files winbind sss
九、修改 /etc/pam.d/system-auth、/etc/pam.d/password-auth,增加下列設定:
session required pam_mkhomedir.so
[如果已使用 setup 設定完成,請跳第至十四步驟]
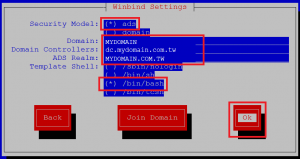
十、(如果沒有setup可用) /etc/samba/smb.conf 設定:
[global]
workgroup = MYDOMAIN
password server = dc.mydomain.com.tw
realm = MYDOMAIN.COM.TW
security = ads
idmap config * : range = 16777216-33554431
template shell = /bin/bash
winbind use default domain = false
winbind offline logon = false
server string = Samba Server Version %v
log file = /var/log/samba/log.%m
max log size = 50
passdb backend = tdbsam
load printers = no
cups options = raw
encrypt passwords = yes
winbind enum users = yes
winbind enum groups = yes
template homedir = /home/%D/%U
十一、(如果沒有setup可用) /etc/krb5.conf 設定:
[libdefaults]
default_realm = MYDOMAIN.COM.TW
dns_lookup_realm = false
dns_lookup_kdc = false
ticket_lifetime = 24h
renew_lifetime = 7d
forwardable = true
[realms]
EXAMPLE.COM = {
kdc = kerberos.example.com
admin_server = kerberos.example.com
}
MYDOMAIN.COM.TW = {
kdc = dc.mydomain.com.tw
}
[domain_realm]
.example.com = EXAMPLE.COM
example.com = EXAMPLE.COM
十二、(如果沒有setup可用) /etc/pam.d/system-auth 設定:
auth required pam_env.so
auth sufficient pam_fprintd.so
auth sufficient pam_unix.so nullok try_first_pass
auth requisite pam_succeed_if.so uid >= 500 quiet
auth sufficient pam_winbind.so use_first_pass
auth required pam_deny.so
account required pam_unix.so broken_shadow
account sufficient pam_localuser.so
account sufficient pam_succeed_if.so uid < 500 quiet
account [default=bad success=ok user_unknown=ignore] pam_winbind.so
account required pam_permit.so
password requisite pam_cracklib.so try_first_pass retry=3 type=
password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok
password sufficient pam_winbind.so use_authtok
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
session optional pam_oddjob_mkhomedir.so umask=0077
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.so
session required pam_mkhomedir.so
十三、(如果沒有setup可用) /etc/pam.d/password-auth 設定:
auth required pam_env.so
auth sufficient pam_unix.so nullok try_first_pass
auth requisite pam_succeed_if.so uid >= 500 quiet
auth sufficient pam_winbind.so use_first_pass
auth required pam_deny.so
account required pam_unix.so broken_shadow
account sufficient pam_localuser.so
account sufficient pam_succeed_if.so uid < 500 quiet
account [default=bad success=ok user_unknown=ignore] pam_winbind.so
account required pam_permit.so
password requisite pam_cracklib.so try_first_pass retry=3 type=
password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok
password sufficient pam_winbind.so use_authtok
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
session optional pam_oddjob_mkhomedir.so umask=0077
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.so
session required pam_mkhomedir.so
十四、修改 /etc/security/pam_winbind.conf,增加下列設定:
require_membership_of = S-1-5-21-1111111111-1111111111-1111111111-111 (Domain Admins 的 SID,限制Domain Admins的成員才能登入)
如果要加入多重群組或帳號,則用逗號分隔:
require_membership_of = S-1-5-21-1111111111-1111111111-1111111111-111,S-1-5-21-2222222222-2222222222-2222222222-222
十五、增加 sudo 權限:
# visudo
(加入下列設定)
%MYDOMAIN\\domain\ admins ALL=(ALL) NOPASSWD: ALL
十六、與AD校時,然後重新開機:
# ntpdate dc.mydomain.com.tw
# init 6
十七、加入網域:
# net ads join -U ADMINS_USER_ID
Enter Administrator’s password:
Using short domain name — MYDOMAIN
Joined ‘myhost’ to dns domain ‘mydomain.com.tw’
十八、重啟服務:
# systemctl restart smb
# systemctl restart winbind
十九、確認是否正確加入網域:
# net ads info (會看到 AD 的相關資訊)
# getent group (會看到 MYDOMAIN\GROUP 的網域群組)
(下列指令如果使用者幾萬或幾十萬筆,就不要用了,會等很久)
# wbinfo -u (會看到 MYDOMAIN\USERID 的使用者帳號)
# getent passwd (會看到 MYDOMAIN\USERID 的使用者帳號)
二十、這樣就可以正常使用 MYDOMAIN\userID 登入
